Why choose Zero Trust Web Access?
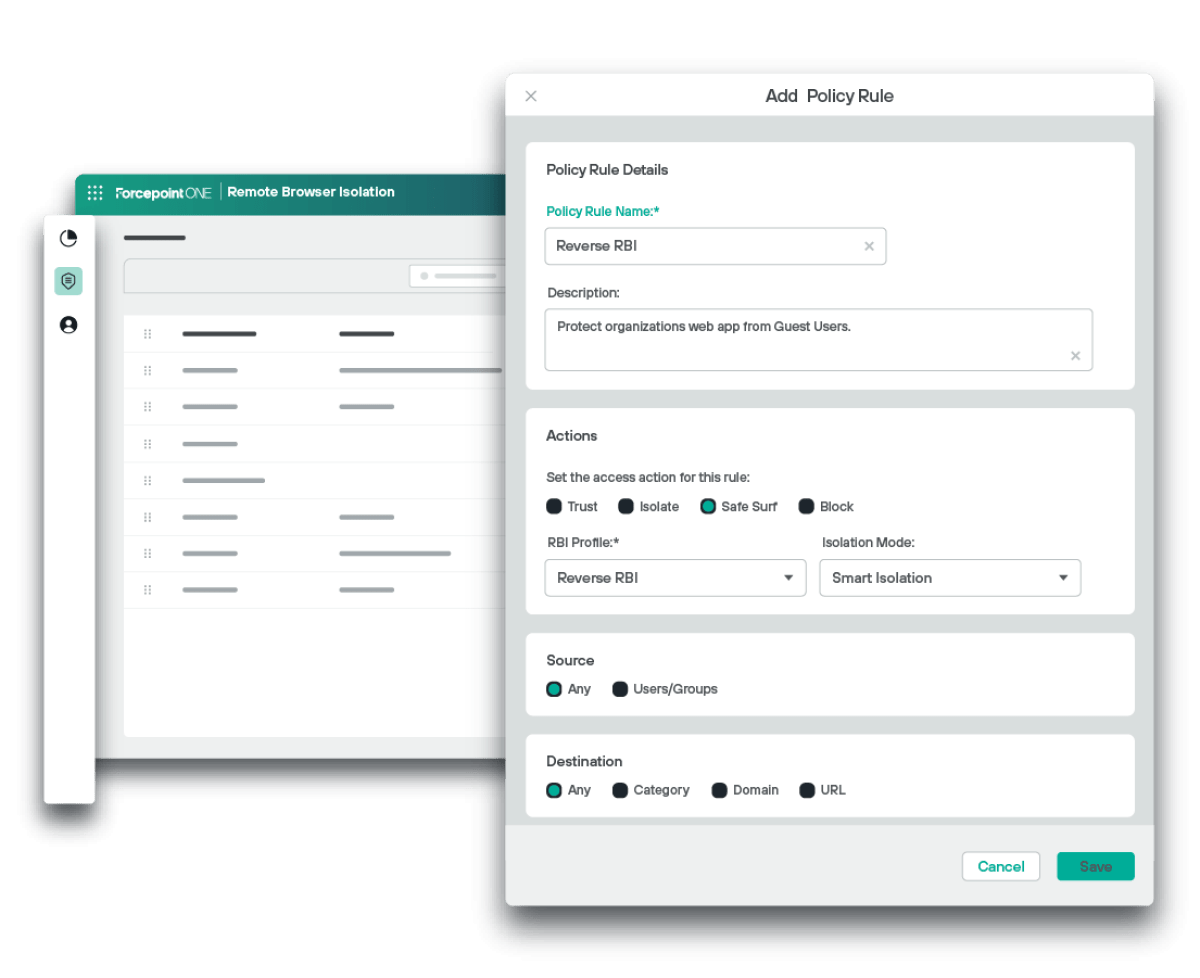
Remote Browser Isolation Use Cases
Prevent Phishing Attacks
RBI isolates all risky URLs and uses read-only mode functionality to automatically prevent credential threat from high-risk destinations.
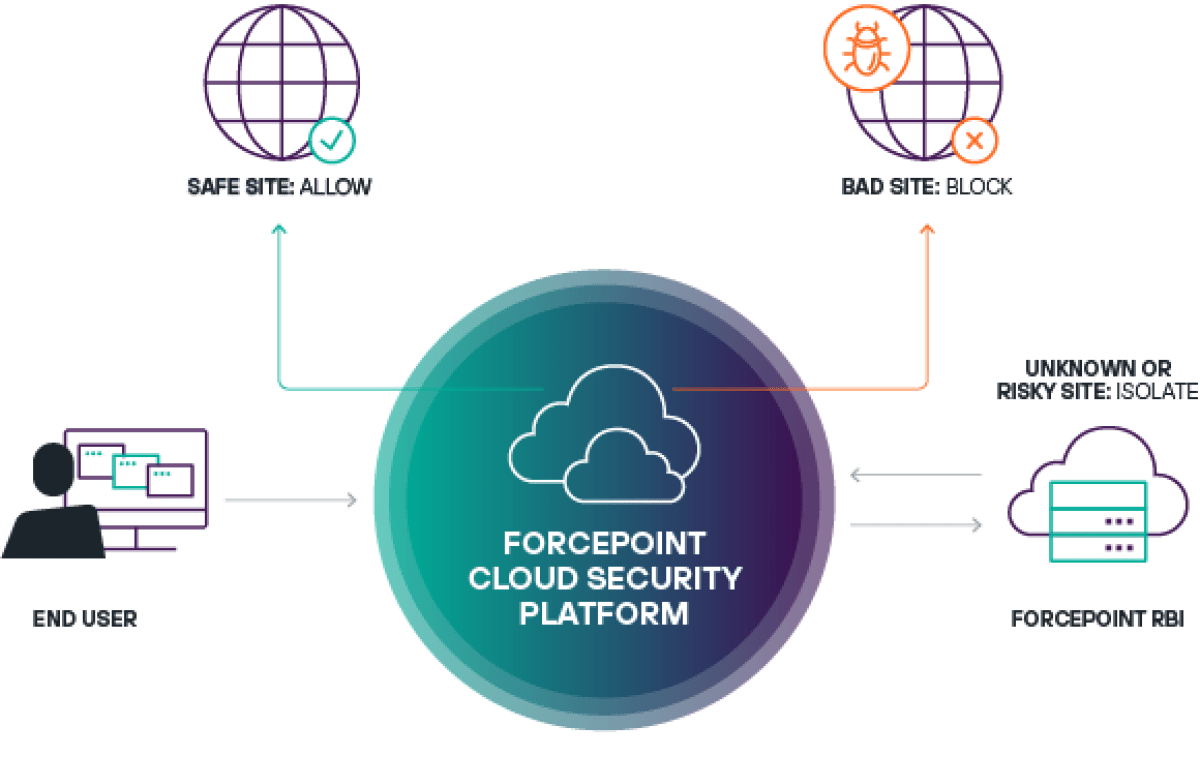
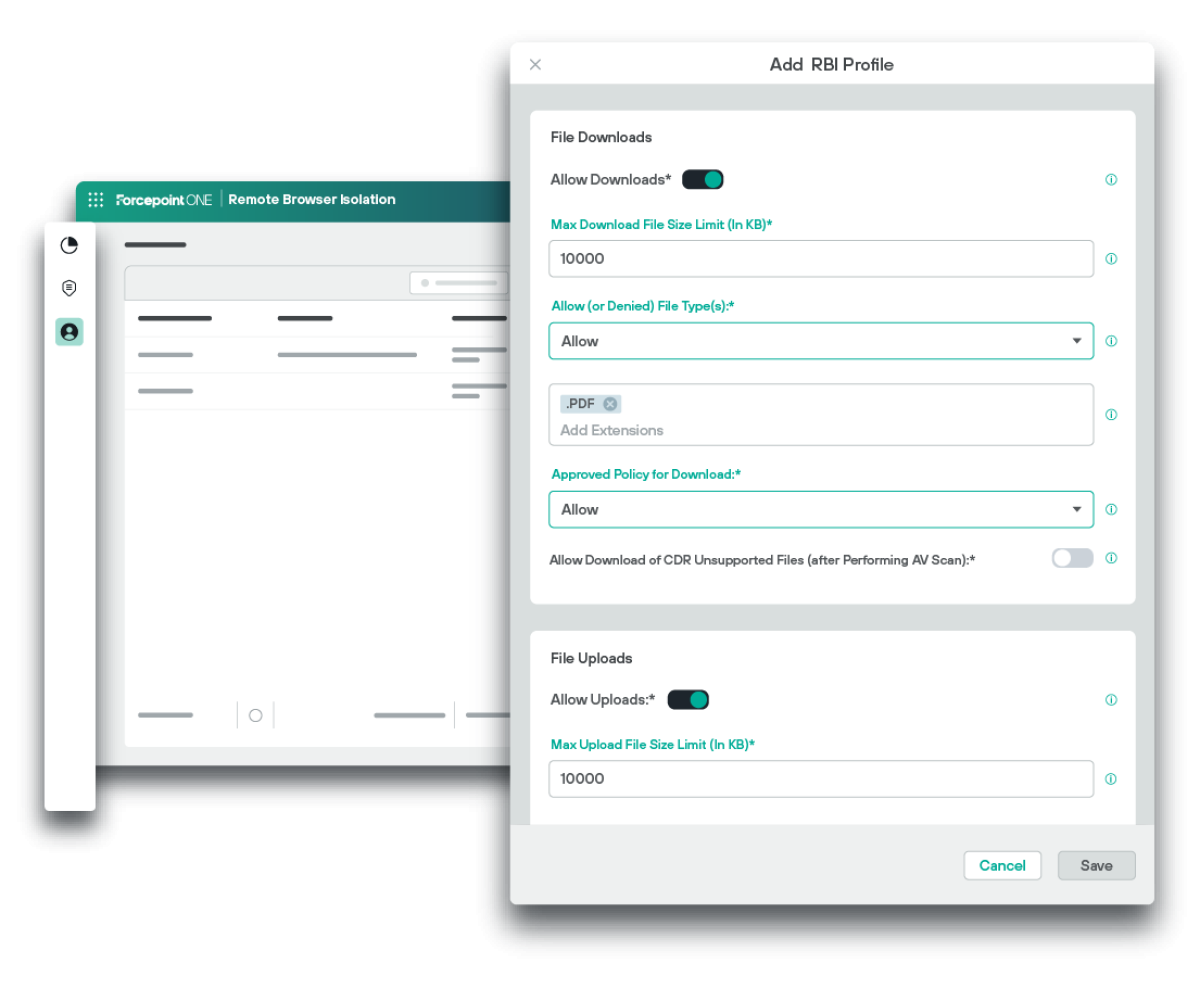
Protect Data from Theft
Threat actors can encrypt data inside of images to exfiltrate it outside of the network – and this steganographic attack is difficult to prevent with traditional antivirus. RBI uses Zero Trust CDR to sanitise all images before they are uploaded to prevent steganographic data loss.
Secure BYOD from Malware
Bring Your Own Device (BYOD) carries a high risk for malware to be introduced unknowingly into the network through a user’s personal device. Control clipboard and print access, as well as uploads and downloads for specific destinations, using reverse RBI.
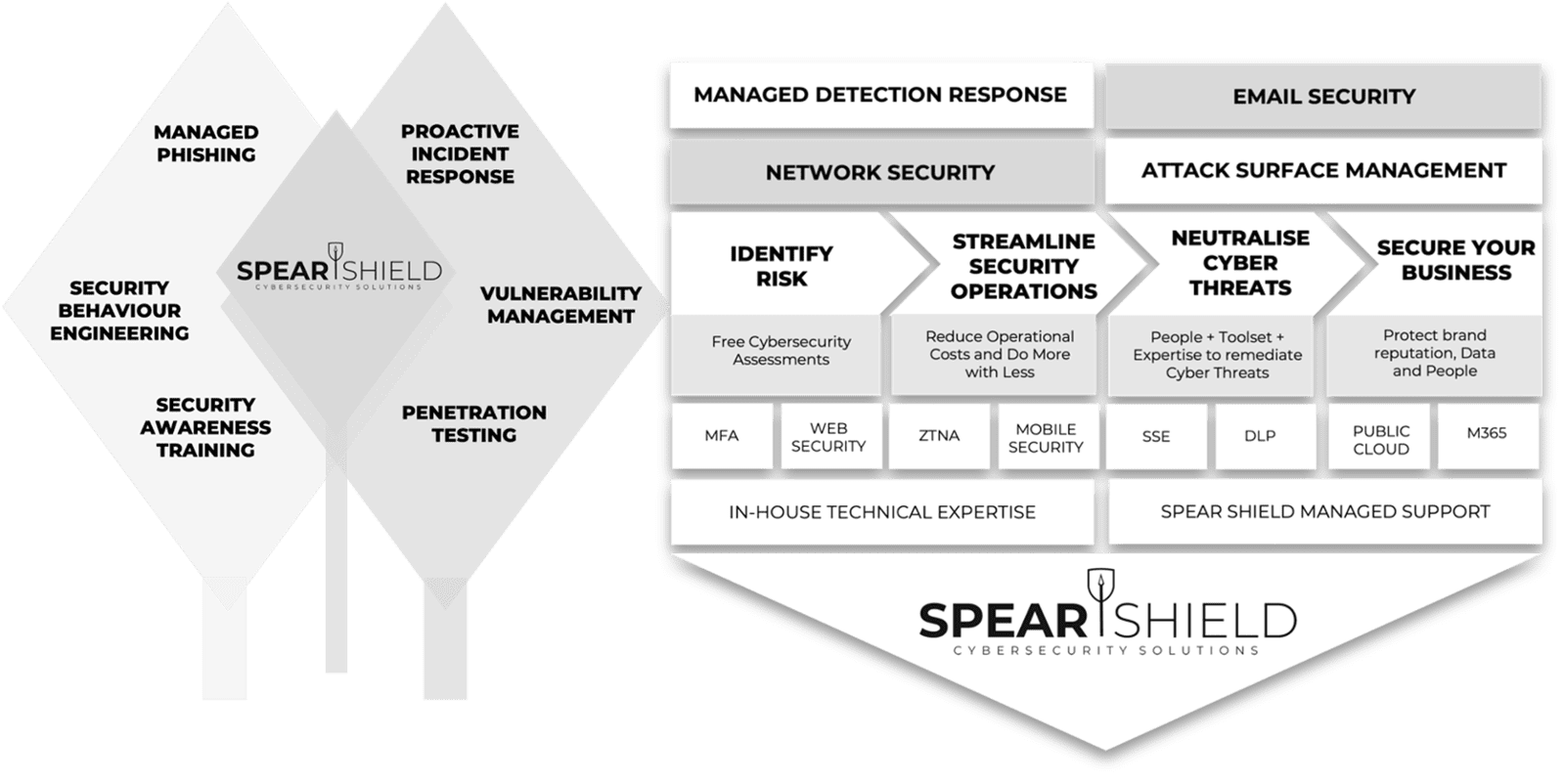
Achieving Security Outcomes Together
Mitigating Human-Activated Risk
Associate Director (Information and Security) Concertus, part of the Vertas Group.
Enhancing SecOps with 24/7 MDR
Head of I.T, Times Higher Education
IT Security validation with Penetration Testing
VIDEO COMING SOON
Achieving Supplier Assurance with Cyber Essentials Plus

'We're delighted with our data security efforts - we're Cyber Essentials Plus certified!
This wouldn't have been possible without the help of Spear Shield, trusted local cybersecurity experts here in Ipswich. As part of our commitment to safe recruiting, secure sensitive data is crucial. This certification proves our proactive measures to prevent cyber risks."
I.T Manager, Sanctuary Personnel
Understanding Human Risk with SAT
VIDEO COMING SOON
Why customers Secure with Spear Shield
FAQ's
Everything you need to know about Spear Shield.