Detect Network Behaviours to help identify:
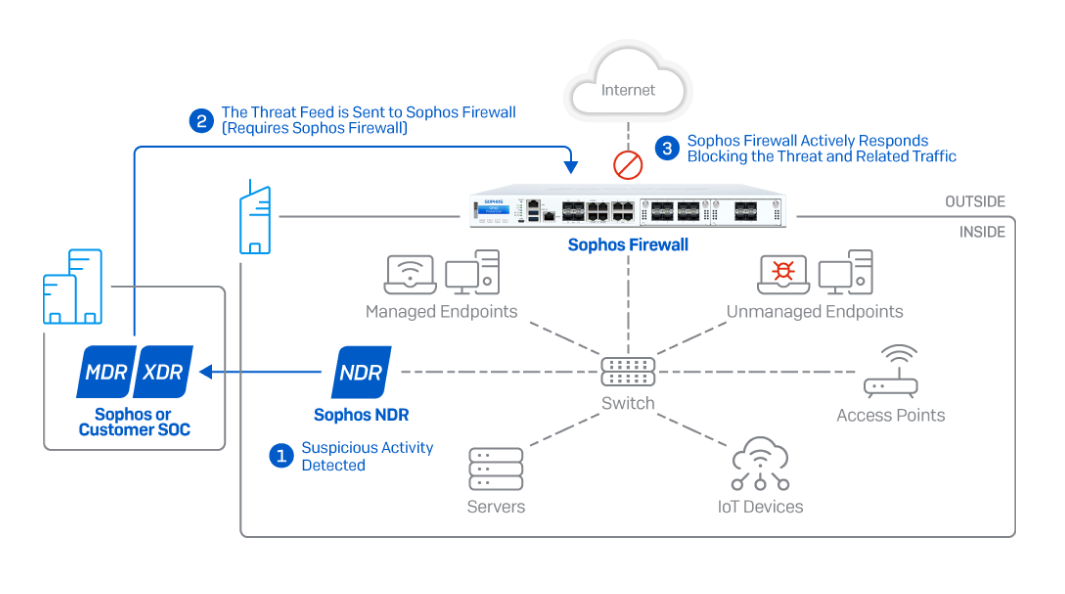
How does it work?
NDR monitors traffic deep within your network, sending suspicious activity to your Sophos Central data lake for further analysis. In the event of an active threat or if an adversary is identified, analysts can immediately push a threat feed to your Sophos Firewall that can coordinate an Active Threat Response to isolate and block malicious activity, automatically and in real-time.
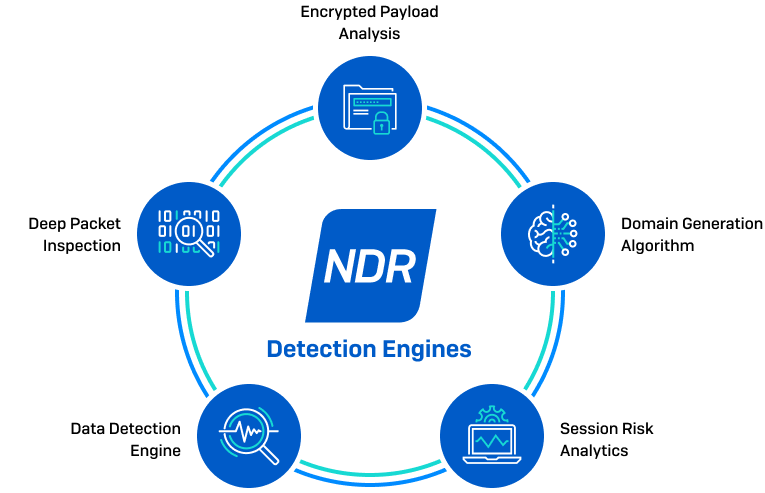
Data Detection Engine
Extensible query engine uses a deep learning prediction model to analyse encrypted traffic and identify patterns across unrelated network flows.
Deep Packet Inspection
Uses known indicators of compromise to identify threat actors and malicious tactics, techniques, and procedures across encrypted and unencrypted network traffic.
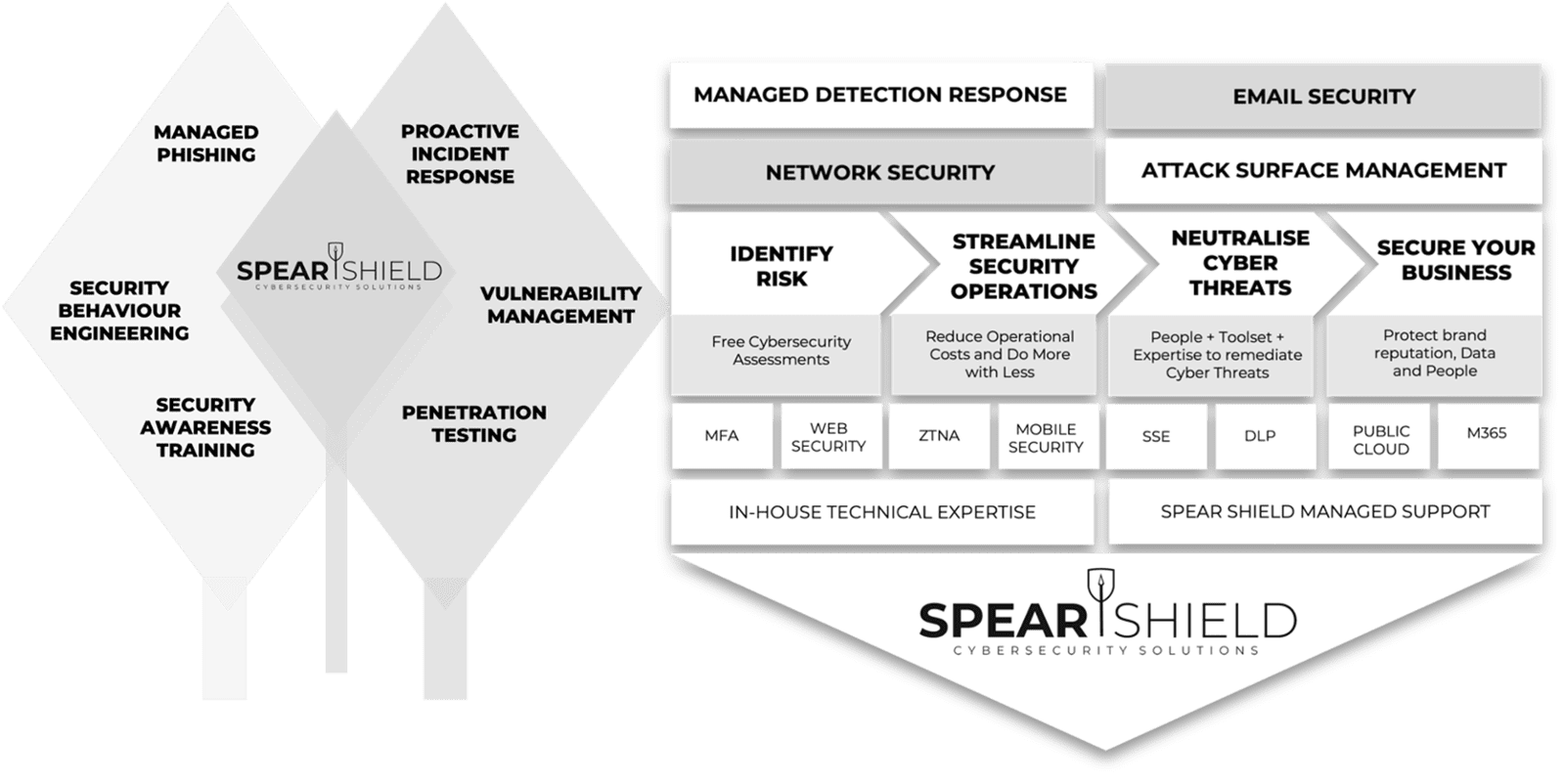
Achieving Security Outcomes Together
Mitigating Human-Activated Risk
Associate Director (Information and Security) Concertus, part of the Vertas Group.
Enhancing SecOps with 24/7 MDR
Head of I.T, Times Higher Education
IT Security validation with Penetration Testing
VIDEO COMING SOON
Achieving Supplier Assurance with Cyber Essentials Plus

'We're delighted with our data security efforts - we're Cyber Essentials Plus certified!
This wouldn't have been possible without the help of Spear Shield, trusted local cybersecurity experts here in Ipswich. As part of our commitment to safe recruiting, secure sensitive data is crucial. This certification proves our proactive measures to prevent cyber risks."
I.T Manager, Sanctuary Personnel
Understanding Human Risk with SAT
VIDEO COMING SOON
Why customers Secure with Spear Shield
FAQ's
Everything you need to know about Spear Shield.