Why is Shadow IT important?
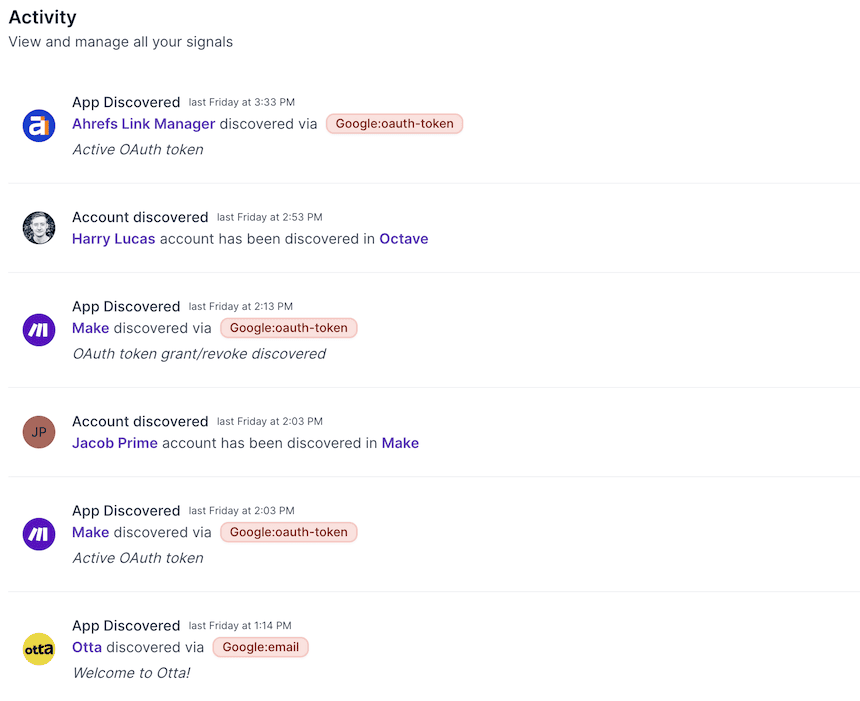
How does Shadow IT Work and what next?
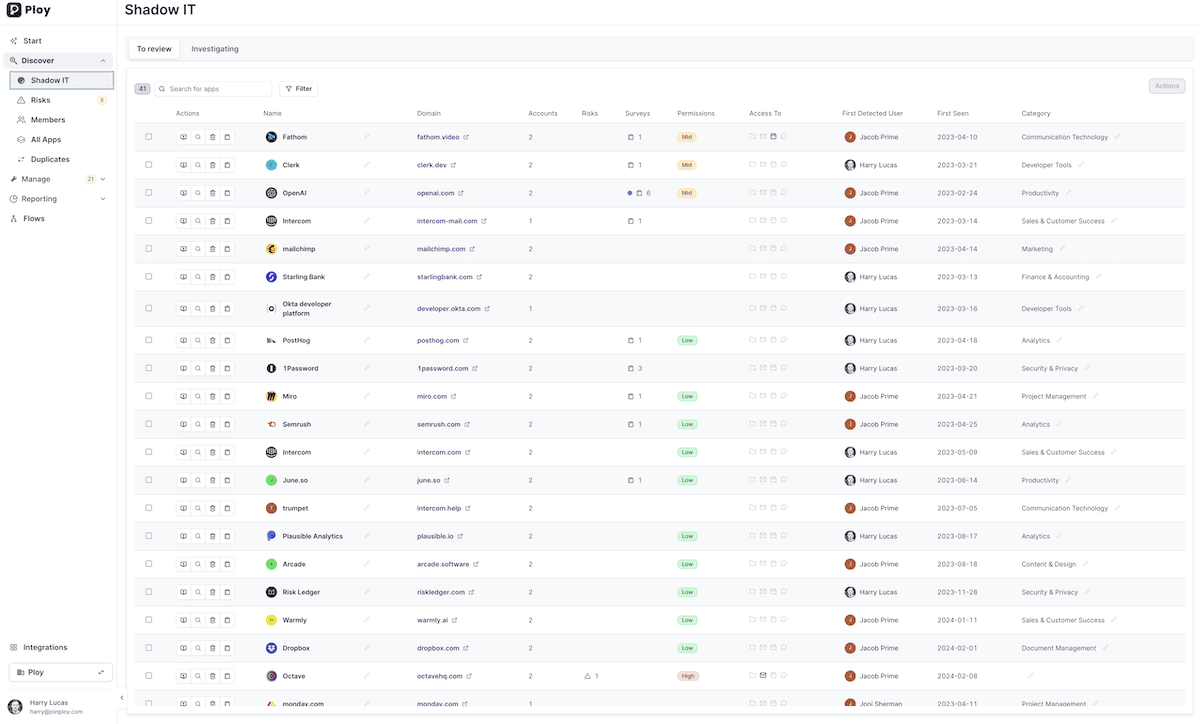
Gain Full Visibility in ~5 Minutes
Gain Full Visibility in ~5 Minutes
- No Complicated Set-up Process
- No Agents to deploy or complex configuration
- Integrate your core IdP accounts... and that's it!
- No Complicated Set-up Process
- No Agents to deploy or complex configuration
- Integrate your core IdP accounts... and that's it!
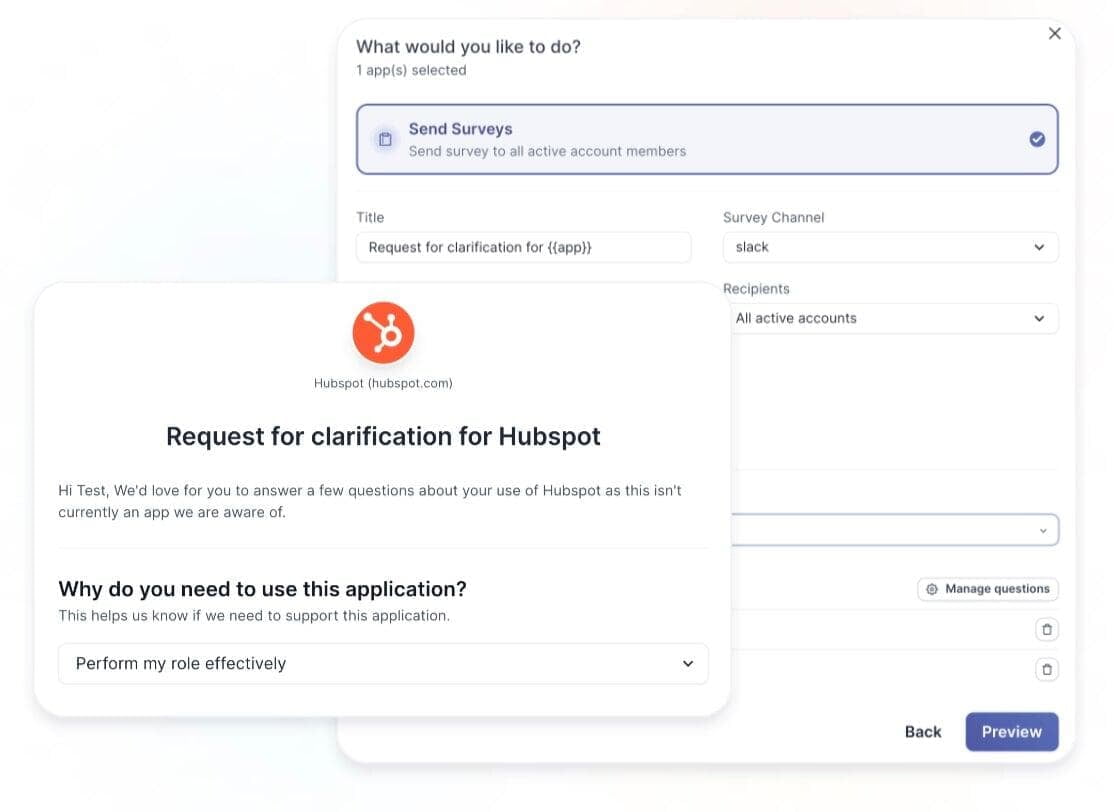
2-Click Surveys
Once you've discovered your Apps, Next, quickly understand the 'why' behind employee tool choices. In just two clicks, launch surveys directly through Microsoft Teams or Slack to get insights from your users without disrupting workflow.
Workflow Builder
Benefit from a dynamic workflow builder designed to adapt to your unique business needs. Build custom access management workflows or jump-start your automation journey with a comprehensive template library. Use cases include Onboarding/Off-boarding, detection of new high risk apps and permissions, spend monitoring and more.
Request a demo to learn more
Achieving Security Outcomes Together
Mitigating Human-Activated Risk
Associate Director (Information and Security) Concertus, part of the Vertas Group.
Enhancing SecOps with 24/7 MDR
Head of I.T, Times Higher Education
IT Security validation with Penetration Testing
VIDEO COMING SOON
Achieving Supplier Assurance with Cyber Essentials Plus

'We're delighted with our data security efforts - we're Cyber Essentials Plus certified!
This wouldn't have been possible without the help of Spear Shield, trusted local cybersecurity experts here in Ipswich. As part of our commitment to safe recruiting, secure sensitive data is crucial. This certification proves our proactive measures to prevent cyber risks."
I.T Manager, Sanctuary Personnel
Understanding Human Risk with SAT
VIDEO COMING SOON
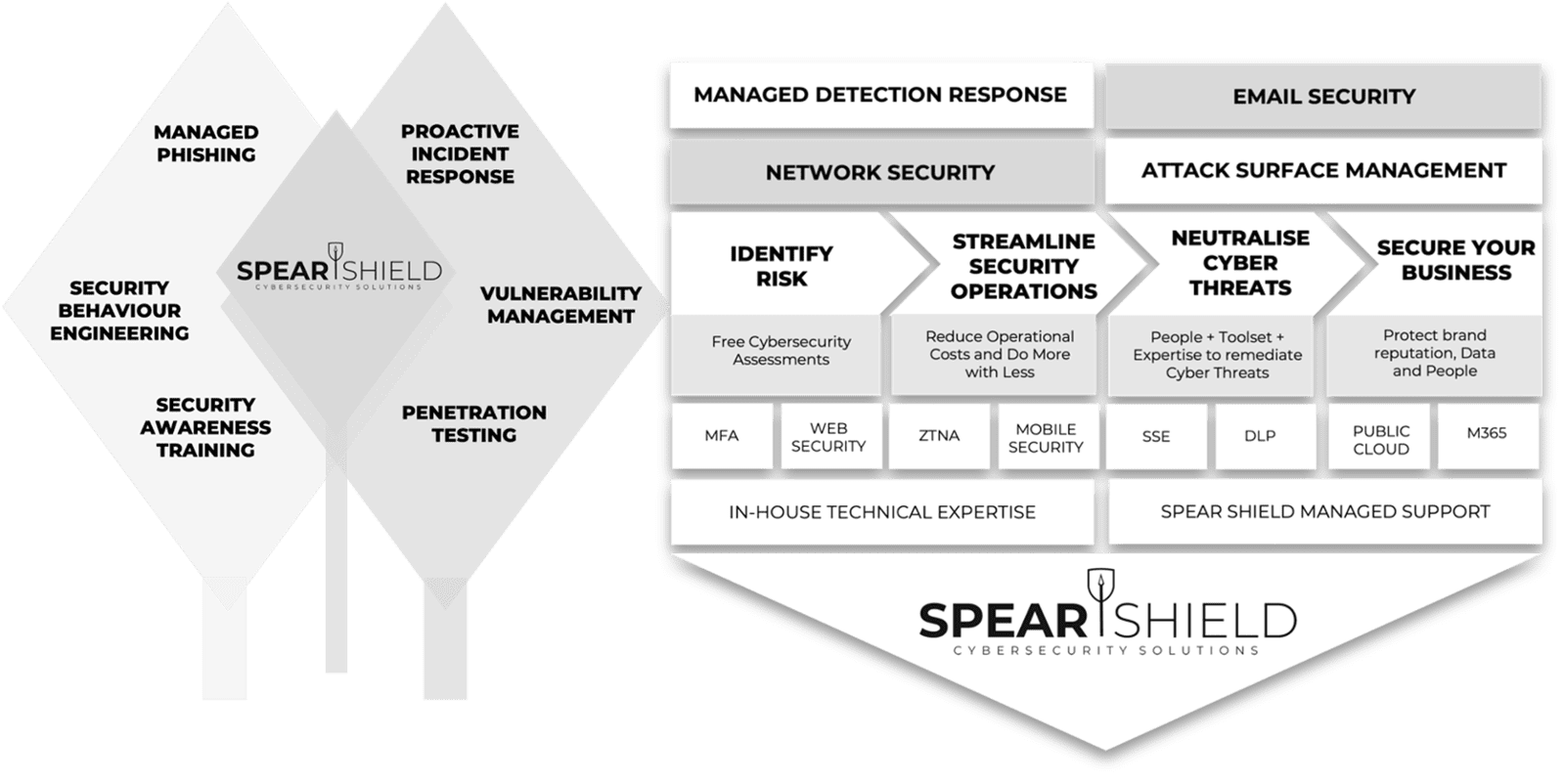
Why customers Secure with Spear Shield
FAQ's
Everything you need to know about Spear Shield.