The Ultimate Remote Access VPN Replacement
How does it work?
Available as a virtual appliance on Hyper-V, VMware, and Amazon Web Services, ZTNA is easy to deploy. It makes your applications invisible to the public internet while providing a secure connection for verified users and their validated devices to the applications they need to do their job.
Enhanced Security
ZTNA eliminates vulnerable VPN clients, integrates device health, and removes the implicit trust and broad network access that VPN provides. It allows granular access to resources defined by policies based on health and identity to enhance your security posture.
Easy Management
ZTNA is built to scale quickly and easily, unlike old-school VPN. It's cloud-delivered and cloud-managed in Sophos Central. Sophos ZTNA offers a unique single-agent, single-console, and single-vendor solution with Sophos Intercept X for easy deployment and management.
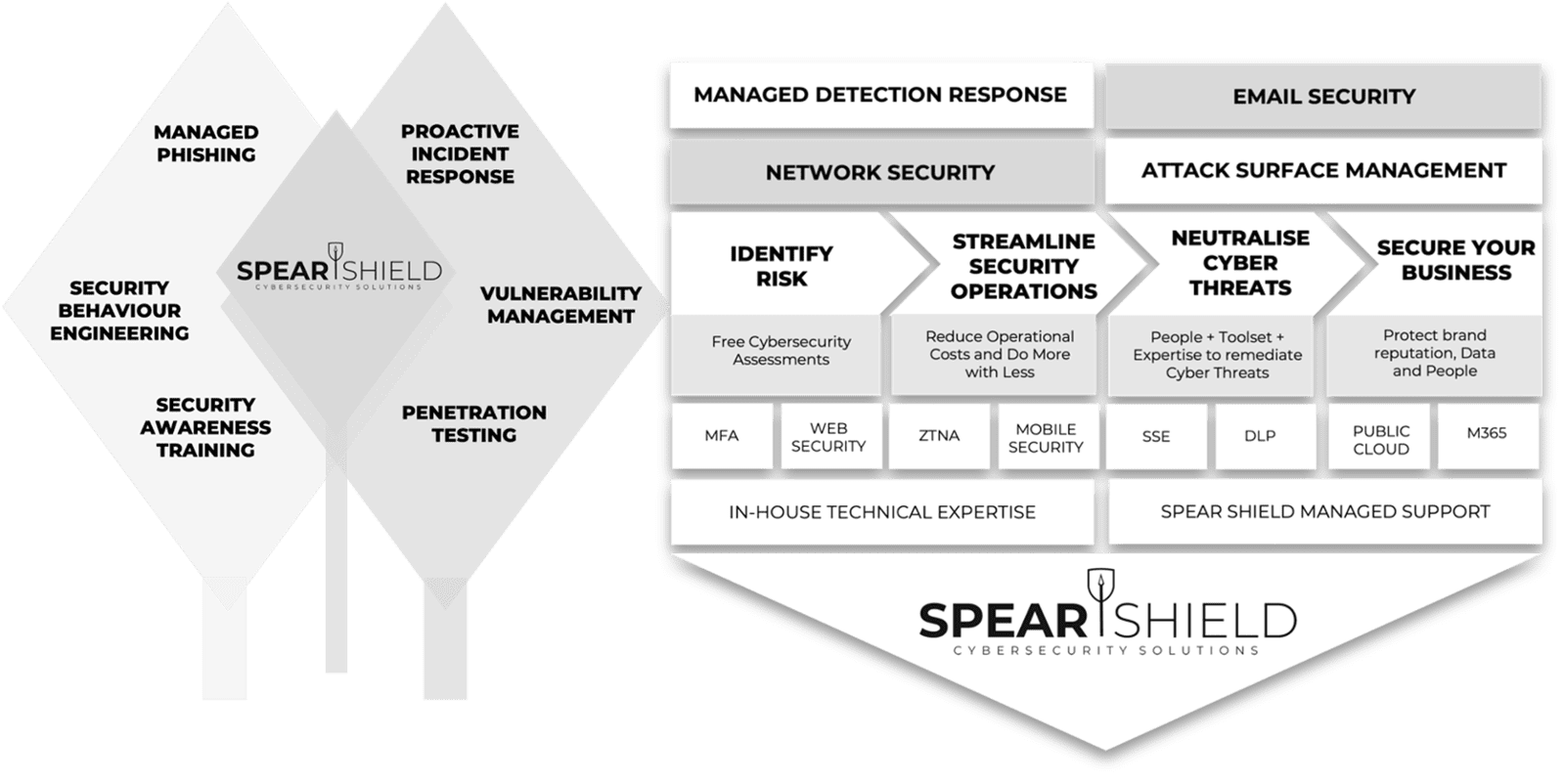
Achieving Security Outcomes Together
Mitigating Human-Activated Risk
Associate Director (Information and Security) Concertus, part of the Vertas Group.
Enhancing SecOps with 24/7 MDR
Head of I.T, Times Higher Education
IT Security validation with Penetration Testing
VIDEO COMING SOON
Achieving Supplier Assurance with Cyber Essentials Plus

'We're delighted with our data security efforts - we're Cyber Essentials Plus certified!
This wouldn't have been possible without the help of Spear Shield, trusted local cybersecurity experts here in Ipswich. As part of our commitment to safe recruiting, secure sensitive data is crucial. This certification proves our proactive measures to prevent cyber risks."
I.T Manager, Sanctuary Personnel
Understanding Human Risk with SAT
VIDEO COMING SOON
Why customers Secure with Spear Shield
FAQ's
Everything you need to know about Spear Shield.